Set up Stomio for Managers in your Okta organization.
Contents
- Supported features
- Requirements
- Configuration steps
- Logging into Stomio using Okta
- Advanced topics
Supported Features
- Service Provider (SP) initiated sign in flow: The authentication occurs when the user attempts to log in to the application from Stomio.
- Identity Provider (IdP) initiated sign in flow: The authentication occurs when the user attempts to log in to the application from the Okta dashboard.
Requirements
- Admin access to a Stomio workspace
- Admin access to an Okta organization
Configuration Steps
1. Install Stomio for Managers
- In the Okta Dashboard, navigate to Applications.
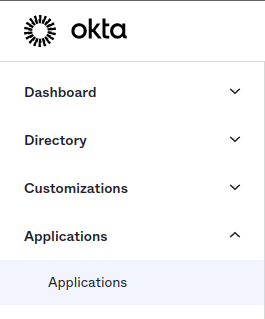 Okta Applications menu
Okta Applications menu
- Click the Browse App Catalog button.
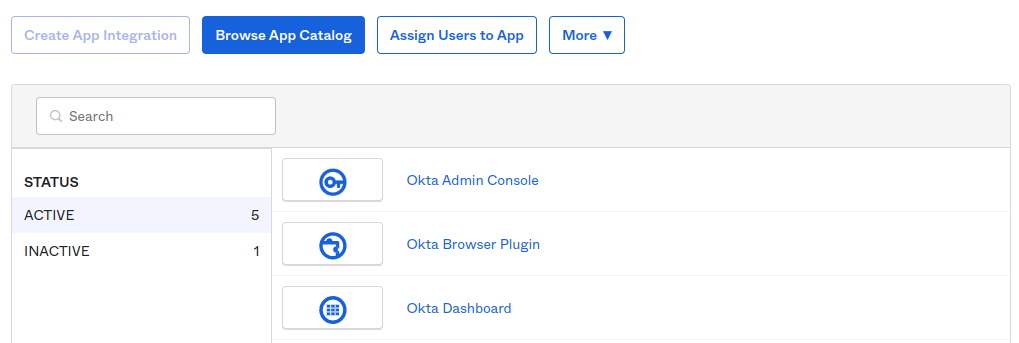 Okta Browse App Catalog button
Okta Browse App Catalog button
- Search for "Stomio for Managers" and select it from the search results.
 Search results for Stomio for managers
Search results for Stomio for managers
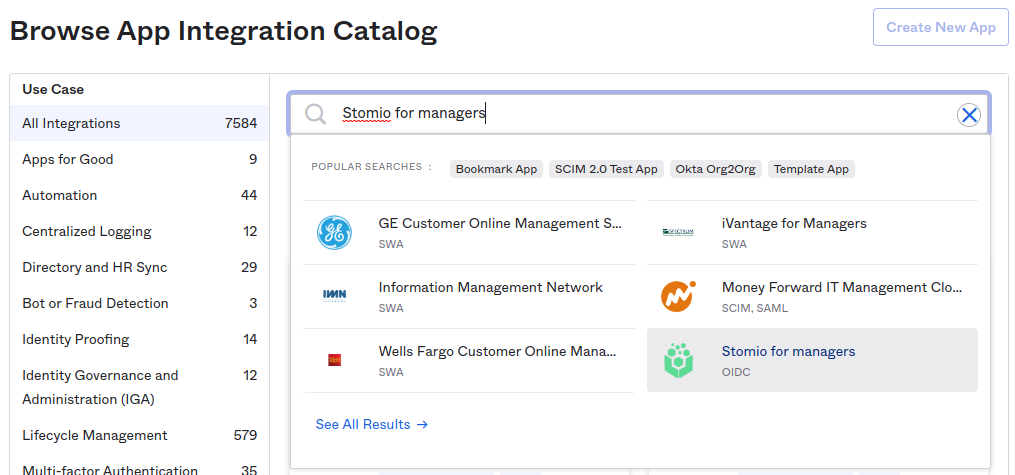
- Click Add Integration to add it to your Okta organization.
 Okta Add Integration screen for Stomio for managers
Okta Add Integration screen for Stomio for managers
- Finish the installation by clicking Done.
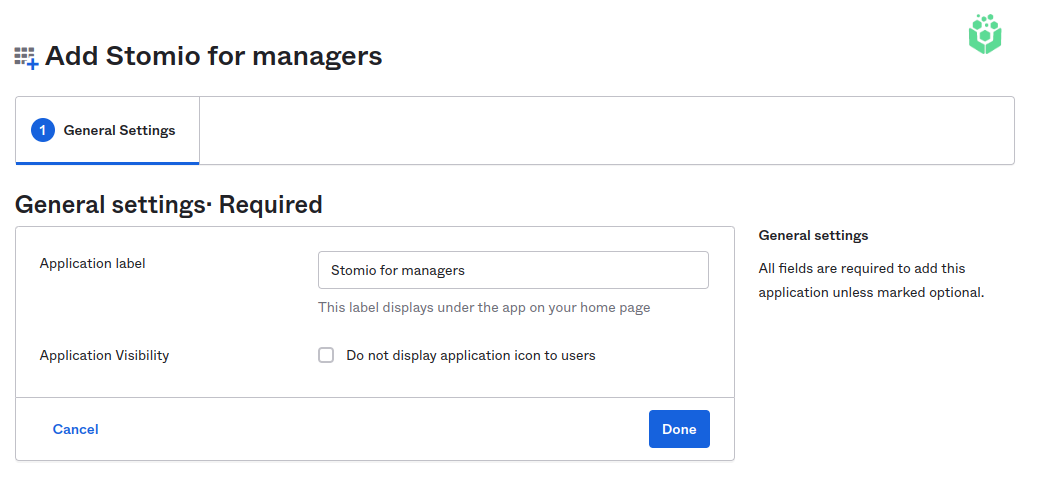 Finish adding Stomio for managers in Okta
Finish adding Stomio for managers in Okta
2. Connect Stomio for Managers Application
- In Stomio, go to Space > Integrations.
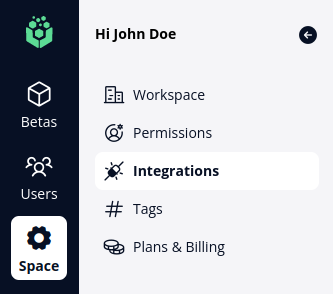 Stomio Space menu showing Integrations
Stomio Space menu showing Integrations
- Click the connect button in the Okta for Managers card under the Single Sign-On section.
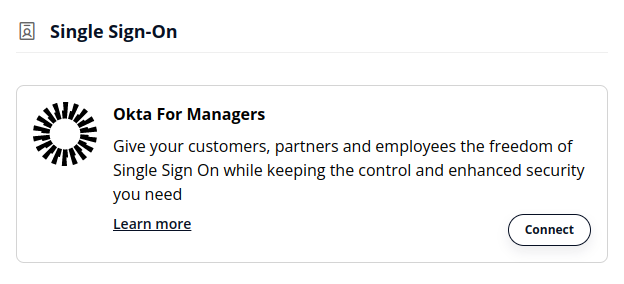 Okta for Managers card in Stomio
Okta for Managers card in Stomio
- In the Okta Dashboard, copy your Okta Organization URL from the top of your profile.
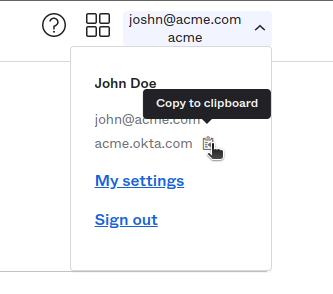 Copy the Okta organization URL from the profile menu
Copy the Okta organization URL from the profile menu
- In Stomio, paste the URL into the corresponding input field.
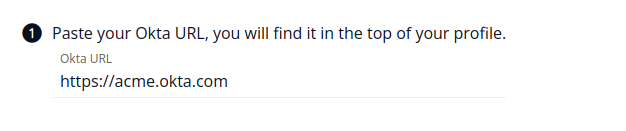 Paste the Okta URL into Stomio
Paste the Okta URL into Stomio
- In the Okta Dashboard, copy the Client ID for your installation of Stomio for Managers (this was moved to Sign On on newer versions of Okta).
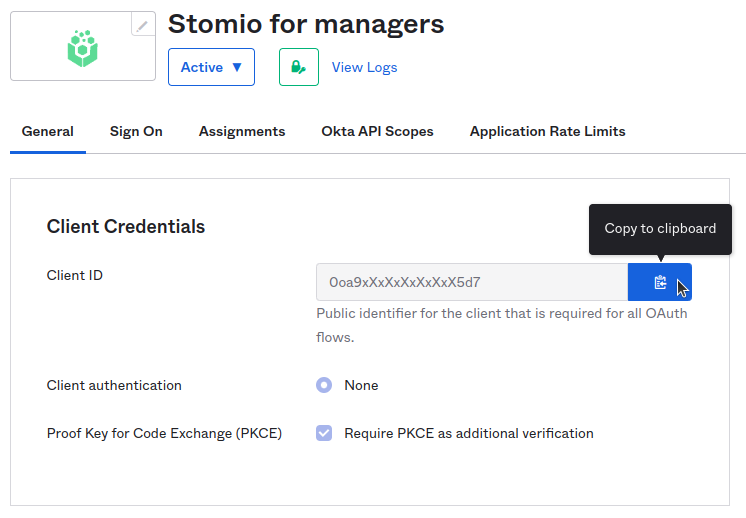 Copy the client ID from the Okta Stomio for managers app
Copy the client ID from the Okta Stomio for managers app
- In Stomio, paste the Client ID.
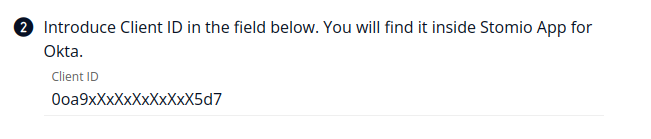 Paste the client ID into Stomio
Paste the client ID into Stomio
3. Grant Cross-Origin Access to Stomio
- In the Okta Dashboard, go to Security > API > Trusted Origins.
- Select Add Origin and enter Stomio as the name for the organization origin.
- In the Origin URL box, paste the Stomio URL:
https://app.stomio.io - Make sure CORS and Redirect are selected. Click Save.
Logging into Stomio using Okta
There are two ways to log into Stomio. Remember to assign the users or groups that should be able to log in.
From Stomio
- In Stomio, copy the link provided on the Okta for Managers setup page.
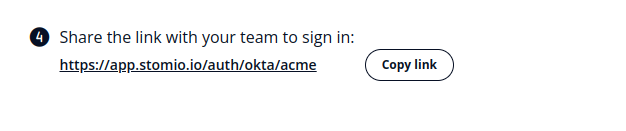 Copy the Stomio Okta sign-in link
Copy the Stomio Okta sign-in link
- Paste the link into your browser's URL bar and press enter.
- You will be redirected to the Okta login page. Enter your credentials.
- If successful, you will be redirected back to Stomio.
From Okta Dashboard
- Log in to your Okta organization.
- Click on the Stomio for Manager icon in the My Apps section.
- You will be redirected to your configured Stomio workspace.
Advanced Topics
How to Map Okta User Attributes to Role in Stomio
Okta admins can optionally map a specific user attribute to a Stomio manager role. Available roles in Stomio:
adminmanagerviewer
Important: This mapping only applies at new manager provisioning through Okta. Once the user is created in Stomio, role changes made by Admins inside Stomio are not synchronized back with the mapping in Okta.
Steps:
- Decide what user attribute you want to use to map to Stomio's Role (e.g., a custom organization "Role" attribute).
- Add a custom attribute
stomio_roleof typestringto the appuser of the Stomio app.
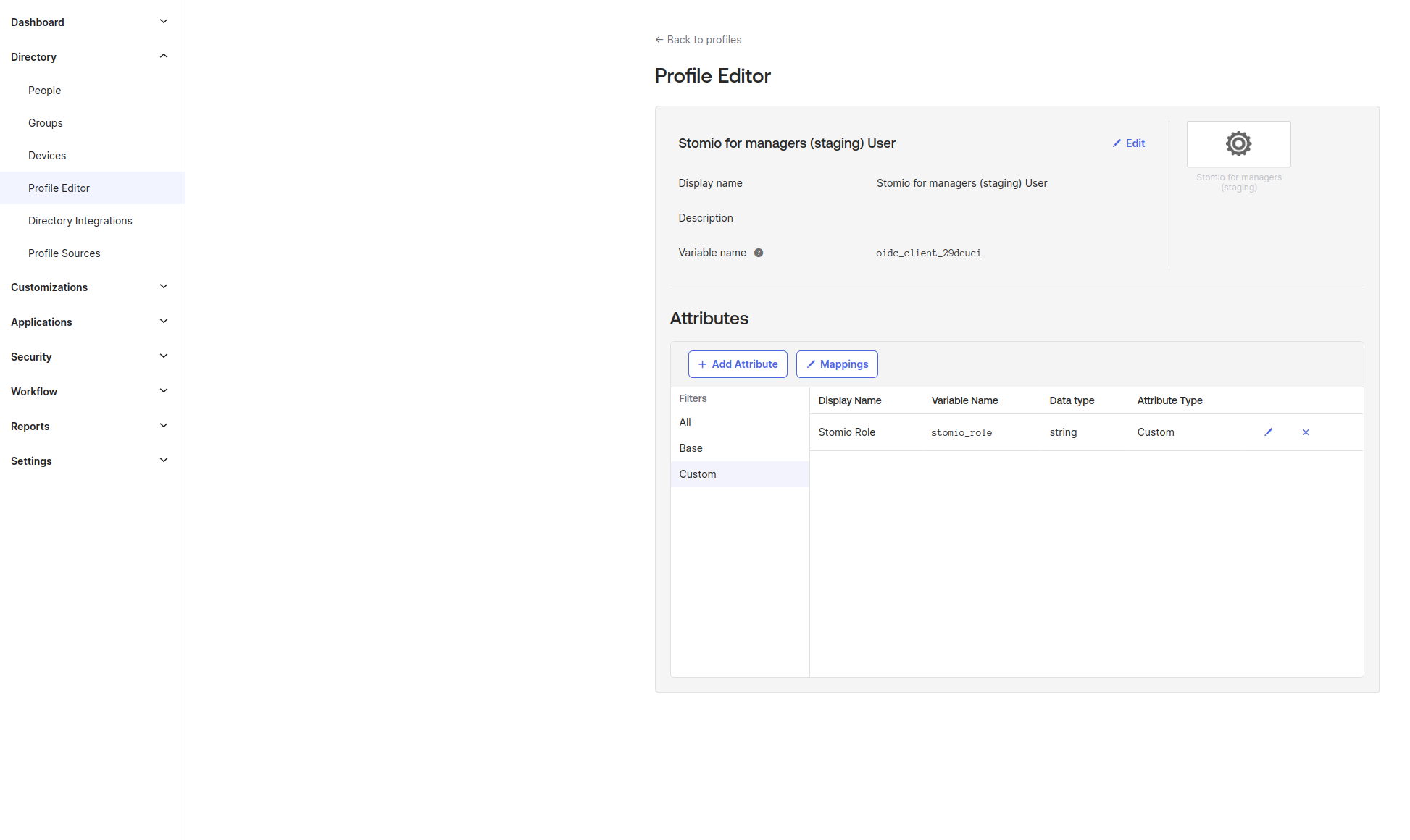 Okta Profile Editor showing the stomio_role custom attribute
Okta Profile Editor showing the stomio_role custom attribute
- Map the custom user attribute to the
stomio_roleattribute.
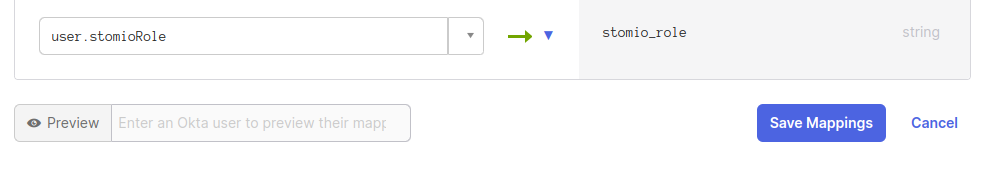 Okta mapping from a custom user attribute to stomio_role
Okta mapping from a custom user attribute to stomio_role
- Once mapped, depending on the value of the custom attribute, the user will be assigned the corresponding role in Stomio upon provisioning.
- Values must match exactly:
admin,manager, orviewer. If not, the default rolemanagerwill be used.
How to Reserve a Specific Domain
To prevent users from creating a separate workspace using a specific email domain, contact Stomio support to verify and add the domain to your workspace.